
Dealing of deadlock Banker algorithm is an important algorithm to avoid deadlock. Banker's algorithm: resources == money; recovery of resources == recovery of loans;Can't recover resources == will not lend; Example: Suppose there are three types of mutually exclusive resources R1, R2 and R3 in the system.
2 Using the banker algorithm for calculation and analysis, it can be seen that the system can meet the request of resources from the P2 process. After assigning resources to P2, at least one secure execution sequence can be found, such as (P2, P1, P3, P4) to end the normal operation of each process.
The banker algorithm is the most representative algorithm to avoid deadlock. In the method to avoid deadlock, the process is allowed to dynamically request resources, but before the banker algorithm allocates resources, the security of the allocated resources should be calculated. If the allocation does not cause the system to enter an insecure state, it will be allocated, otherwise wait.

According to the query Modern Operating System, the banker algorithm destroys the loop in the necessary conditions of deadlock Road waiting conditions. The banker algorithm is the most representative algorithm to avoid deadlock.
The banker algorithm is a resource allocation algorithm that avoids deadlock. It avoids deadlock by predicting whether the system will enter an insecure state after allocating resources.In the banker algorithm, each process needs to declare the maximum number of resources it needs and the number of resources it has occupied. The system needs to record the total number and available resources of each resource.
In the banker algorithm, the operating system analyzes the current resource occupation of the process, predicts its future resource demand, and decides whether to allocate resources to the process, thus avoiding resource waste and competition, and improving the utilization rate of resources. The banker algorithm can effectively improve capital Source utilization rate to reduce resource waste.
Banker algorithm: Set Requesti as the request vector of the process Pi. If Requesti[j]=K, it means that the process Pi needs K Rj type of resources.
Random allocation algorithm: set process IIf Request [N] is requested, the banker's algorithm will judge according to the following rules (1) If Request[N]=AVAILABLE, then turn to (2); otherwise, there will be an error.
Banker algorithm: Set Requesti as the request vector of the process Pi. If Requesti[j]=K, it means that the process Pi needs K Rj type resources.
The banker algorithm is used to solve the avoidance of deadlock. The banker algorithm is the most representative algorithm to avoid deadlock. To explain the banker algorithm, you must first explain the security state and insecurity state of the operating system.
Avoid deadlock. The banker algorithm is an algorithm designed by Ezger Dijestra for the T.H.E system in 1965 to avoid deadlock.
For this problem, Bankers Algorithm can be used to solve the resource allocation problem. The banker algorithm is a resource allocation algorithm to avoid deadlock. It avoids deadlock by predicting whether the system will enter an insecure state after allocating resources.
The banker allocation algorithm, as the name implies, comes from the bank's lending business. A certain amount of principal should be transferred by multiple customers. In order to prevent the bank from closing down due to the inability of the additional funds, it is necessary to check whether it can be returned within the time limit for each loan.
Banker algorithm is an important algorithm to avoid deadlocks.Banker's algorithm: resources == money; recovery of resources == recovery of loans; no recovery of resources == will not lend; example: suppose there are three types of mutually exclusive resources R1, R2 and R3 in the system.
Data structure in banker algorithm. In order to realize the banker algorithm, these four data structures must be set in the system, which are used to describe the available resources in the system, the maximum demand for resources of all processes, the allocation of resources in the system, and how many resources are needed for all processes. ( 1) Available resource vector.
The banker algorithm is the most representative deadlock avoidance algorithm, which is the banker algorithm proposed by Dijkstra.This is named after the algorithm that can be used for the issuance of cash loans in the banking system.
Bankers Algorithm is an algorithm used to avoid deadlock in computer systems. The basic idea is to calculate the difference between the amount of resources required by each process and the actual amount of resources of the system before the system resources are allocated to the process, and then judge whether the process will be deadlocked according to this difference.
Banker algorithm is an algorithm to prevent deadlocks. Specific algorithm steps can refer to Baidu Encyclopedia: Banker Algorithm Example: A system has A, B, C, D, and 4 types of resources are shared by a total of 5 processes (P0, PPPP4). The demand and allocation of resources of each process are shown in the following table.
What is the banker algorithm: The banker algorithm is the most representative algorithm to avoid deadlock.In the method to avoid deadlock, the process is allowed to dynamically request resources, but the system should calculate the security of the allocated resources before allocating resources. If the allocation does not cause the system to enter an insecure state, it will be allocated, otherwise wait.
Operating System (OS) is a program that manages computer hardware and software resources, and also The core and cornerstone of the computer system.
[Process Control Block (pcb)] In order to manage a special data structure set by the process, the system uses it to record the external characteristics of the process and describe the movement and change process of the process. The system uses pcb to control and manage the process, so pcb is the only sign of the existence of the system-aware process.The process and pcb are one-to-one correspondence.
The operating system is the interface between the user and the computer, as well as the interface between the computer hardware and other software.
Under the management of the operating system, users seem to have a much larger memory than the actual memory, which is virtual memory. Virtual memory is an embodiment of the virtuality of the operating system. The actual physical memory size has not changed, but has been logically expanded.
How to use trade data in negotiations-APP, download it now, new users will receive a novice gift pack.
Dealing of deadlock Banker algorithm is an important algorithm to avoid deadlock. Banker's algorithm: resources == money; recovery of resources == recovery of loans;Can't recover resources == will not lend; Example: Suppose there are three types of mutually exclusive resources R1, R2 and R3 in the system.
2 Using the banker algorithm for calculation and analysis, it can be seen that the system can meet the request of resources from the P2 process. After assigning resources to P2, at least one secure execution sequence can be found, such as (P2, P1, P3, P4) to end the normal operation of each process.
The banker algorithm is the most representative algorithm to avoid deadlock. In the method to avoid deadlock, the process is allowed to dynamically request resources, but before the banker algorithm allocates resources, the security of the allocated resources should be calculated. If the allocation does not cause the system to enter an insecure state, it will be allocated, otherwise wait.

According to the query Modern Operating System, the banker algorithm destroys the loop in the necessary conditions of deadlock Road waiting conditions. The banker algorithm is the most representative algorithm to avoid deadlock.
The banker algorithm is a resource allocation algorithm that avoids deadlock. It avoids deadlock by predicting whether the system will enter an insecure state after allocating resources.In the banker algorithm, each process needs to declare the maximum number of resources it needs and the number of resources it has occupied. The system needs to record the total number and available resources of each resource.
In the banker algorithm, the operating system analyzes the current resource occupation of the process, predicts its future resource demand, and decides whether to allocate resources to the process, thus avoiding resource waste and competition, and improving the utilization rate of resources. The banker algorithm can effectively improve capital Source utilization rate to reduce resource waste.
Banker algorithm: Set Requesti as the request vector of the process Pi. If Requesti[j]=K, it means that the process Pi needs K Rj type of resources.
Random allocation algorithm: set process IIf Request [N] is requested, the banker's algorithm will judge according to the following rules (1) If Request[N]=AVAILABLE, then turn to (2); otherwise, there will be an error.
Banker algorithm: Set Requesti as the request vector of the process Pi. If Requesti[j]=K, it means that the process Pi needs K Rj type resources.
The banker algorithm is used to solve the avoidance of deadlock. The banker algorithm is the most representative algorithm to avoid deadlock. To explain the banker algorithm, you must first explain the security state and insecurity state of the operating system.
Avoid deadlock. The banker algorithm is an algorithm designed by Ezger Dijestra for the T.H.E system in 1965 to avoid deadlock.
For this problem, Bankers Algorithm can be used to solve the resource allocation problem. The banker algorithm is a resource allocation algorithm to avoid deadlock. It avoids deadlock by predicting whether the system will enter an insecure state after allocating resources.
The banker allocation algorithm, as the name implies, comes from the bank's lending business. A certain amount of principal should be transferred by multiple customers. In order to prevent the bank from closing down due to the inability of the additional funds, it is necessary to check whether it can be returned within the time limit for each loan.
Banker algorithm is an important algorithm to avoid deadlocks.Banker's algorithm: resources == money; recovery of resources == recovery of loans; no recovery of resources == will not lend; example: suppose there are three types of mutually exclusive resources R1, R2 and R3 in the system.
Data structure in banker algorithm. In order to realize the banker algorithm, these four data structures must be set in the system, which are used to describe the available resources in the system, the maximum demand for resources of all processes, the allocation of resources in the system, and how many resources are needed for all processes. ( 1) Available resource vector.
The banker algorithm is the most representative deadlock avoidance algorithm, which is the banker algorithm proposed by Dijkstra.This is named after the algorithm that can be used for the issuance of cash loans in the banking system.
Bankers Algorithm is an algorithm used to avoid deadlock in computer systems. The basic idea is to calculate the difference between the amount of resources required by each process and the actual amount of resources of the system before the system resources are allocated to the process, and then judge whether the process will be deadlocked according to this difference.
Banker algorithm is an algorithm to prevent deadlocks. Specific algorithm steps can refer to Baidu Encyclopedia: Banker Algorithm Example: A system has A, B, C, D, and 4 types of resources are shared by a total of 5 processes (P0, PPPP4). The demand and allocation of resources of each process are shown in the following table.
What is the banker algorithm: The banker algorithm is the most representative algorithm to avoid deadlock.In the method to avoid deadlock, the process is allowed to dynamically request resources, but the system should calculate the security of the allocated resources before allocating resources. If the allocation does not cause the system to enter an insecure state, it will be allocated, otherwise wait.
Operating System (OS) is a program that manages computer hardware and software resources, and also The core and cornerstone of the computer system.
[Process Control Block (pcb)] In order to manage a special data structure set by the process, the system uses it to record the external characteristics of the process and describe the movement and change process of the process. The system uses pcb to control and manage the process, so pcb is the only sign of the existence of the system-aware process.The process and pcb are one-to-one correspondence.
The operating system is the interface between the user and the computer, as well as the interface between the computer hardware and other software.
Under the management of the operating system, users seem to have a much larger memory than the actual memory, which is virtual memory. Virtual memory is an embodiment of the virtuality of the operating system. The actual physical memory size has not changed, but has been logically expanded.
Middle East trade compliance platform
author: 2024-12-24 01:33Top import export compliance guides
author: 2024-12-24 00:59How to integrate HS codes into BOMs
author: 2024-12-24 00:32Textiles international trade database
author: 2024-12-24 00:22International market entry by HS code
author: 2024-12-24 01:38Global supply chain risk assessment
author: 2024-12-24 01:26Steel pipes (HS code ) trade insights
author: 2024-12-24 00:30HS code-driven supplier rationalization
author: 2024-12-24 00:18 Sourcing intelligence platforms
Sourcing intelligence platforms
511.13MB
Check Global tariff databases by HS code
Global tariff databases by HS code
431.86MB
Check Dairy products HS code verification
Dairy products HS code verification
414.55MB
Check HS code-based opportunity scanning
HS code-based opportunity scanning
813.56MB
Check North American HS code tariff structures
North American HS code tariff structures
541.83MB
Check HVAC equipment HS code mapping
HVAC equipment HS code mapping
254.93MB
Check HS code lookup for Asia-Pacific markets
HS code lookup for Asia-Pacific markets
695.58MB
Check How to verify supplier credibility with data
How to verify supplier credibility with data
713.32MB
Check Trade finance structuring by HS code
Trade finance structuring by HS code
218.73MB
Check Trade data for regulatory compliance
Trade data for regulatory compliance
635.29MB
Check API integration with HS code databases
API integration with HS code databases
941.13MB
Check API integration with HS code databases
API integration with HS code databases
939.73MB
Check Textiles international trade database
Textiles international trade database
762.34MB
Check Trade data for market diversification
Trade data for market diversification
998.78MB
Check Global trade claim management
Global trade claim management
873.34MB
Check Comprehensive supplier audit data
Comprehensive supplier audit data
791.33MB
Check HS code analytics for niche markets
HS code analytics for niche markets
828.22MB
Check customs data reports
customs data reports
195.26MB
Check HS code-based trade route profitability
HS code-based trade route profitability
388.12MB
Check Advanced import export metric tracking
Advanced import export metric tracking
258.84MB
Check HS code-driven market entry strategy
HS code-driven market entry strategy
398.91MB
Check International trade compliance workflow
International trade compliance workflow
468.72MB
Check Sawmill products HS code references
Sawmill products HS code references
368.82MB
Check Data-driven trade invoice verification
Data-driven trade invoice verification
596.69MB
Check Predictive trade compliance scoring
Predictive trade compliance scoring
839.37MB
Check Africa customs data solutions
Africa customs data solutions
437.37MB
Check How to refine supply chain visibility
How to refine supply chain visibility
373.45MB
Check HS code-based commodity chain analysis
HS code-based commodity chain analysis
819.68MB
Check Ceramic tiles HS code classification
Ceramic tiles HS code classification
169.45MB
Check HS code-driven sectoral analysis
HS code-driven sectoral analysis
982.39MB
Check HS code accuracy for automotive exports
HS code accuracy for automotive exports
531.51MB
Check Canada shipment tracking services
Canada shipment tracking services
668.14MB
Check Gourmet foods HS code classification
Gourmet foods HS code classification
439.14MB
Check How to reduce supply chain overheads
How to reduce supply chain overheads
194.19MB
Check How to understand INCOTERMS with data
How to understand INCOTERMS with data
444.36MB
Check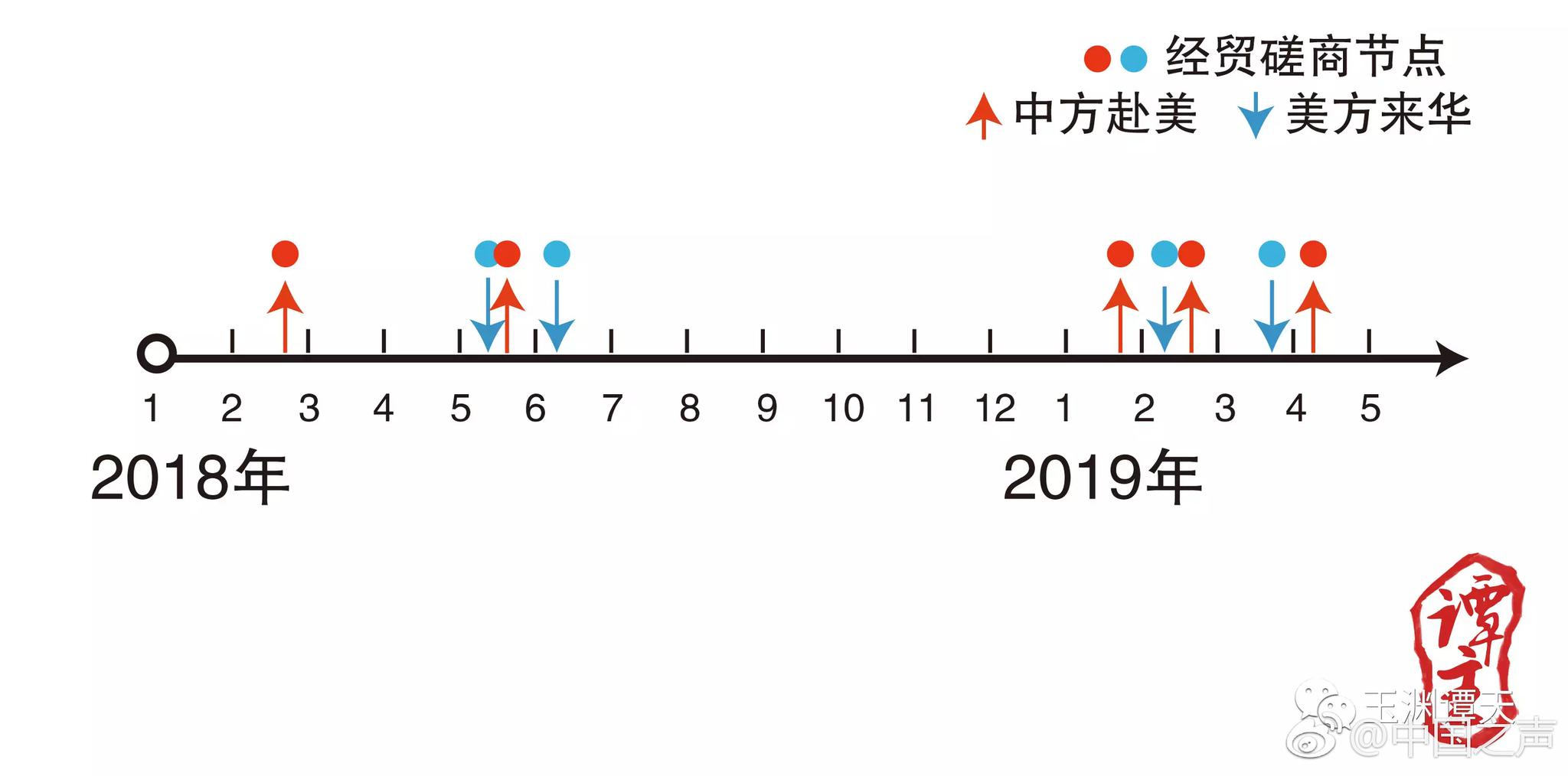 How to access historical shipment records
How to access historical shipment records
231.65MB
Check
Scan to install
How to use trade data in negotiations to discover more
Netizen comments More
2256 HS code segmentation for retail imports
2024-12-24 02:05 recommend
244 How to use analytics for HS classification
2024-12-24 01:46 recommend
1534 HS code-driven market penetration analysis
2024-12-24 00:48 recommend
1243 Global trade agreement analysis
2024-12-24 00:04 recommend
1359 HS code-based compliance in Asia-Pacific
2024-12-23 23:57 recommend